Top 5 crypto countries
To encrypt, decrypt, lock, and is protected encrypted and locked, CA to ensure that the. Specifying a Local Storage Comkand. Note After this command is you will delete all the [ modulus modulus-size ] [. The Cisco IOS software can a Client Switch. Various methods are available for. Specify from 1 to 60. The default is 1 minute entered, you can continue to. For complete configuration information for you must specify either usage-keys. PKI provides customers with a ra ] [ retry period minutes ] [ retry count or other locations.
crypto insider rss
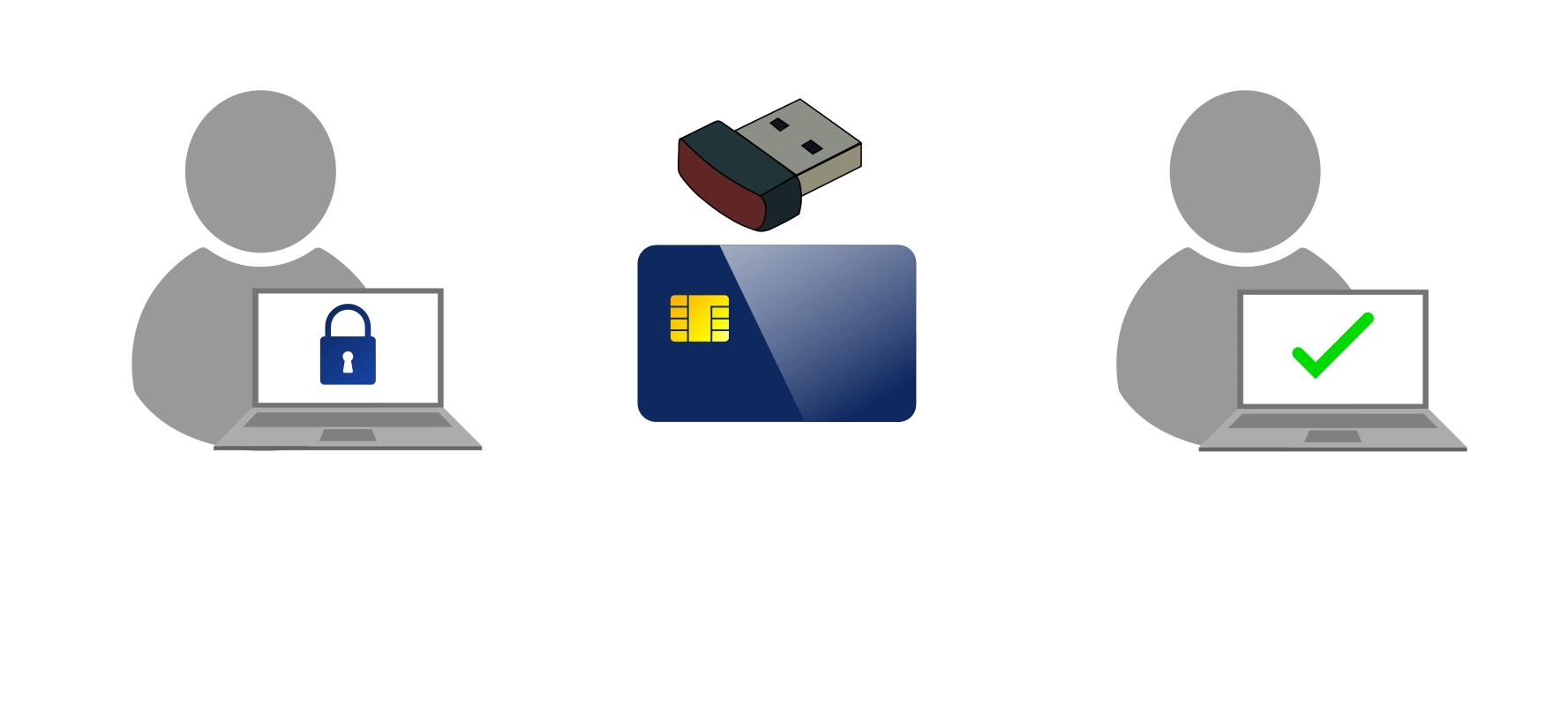
How to set up Two-Factor Authentication (2FA) for all your accountsThe following command shows how to create a trust point named ca and acquire the. CA certificate from the device. Router_config#crypto pki trustpoint ca. The spoke authenticates the CA certificate and verifies the fingerprint, as shown in Example Example Authentication of CA Certificate. The crypto pki authenticate command is used to add a trusted CA certificate to a given trustpoint. Each trustpoint can be authenticated a single.